WO2012010205A1 - A processor-implemented method for ensuring software integrity - Google Patents
A processor-implemented method for ensuring software integrity Download PDFInfo
- Publication number
- WO2012010205A1 WO2012010205A1 PCT/EP2010/060603 EP2010060603W WO2012010205A1 WO 2012010205 A1 WO2012010205 A1 WO 2012010205A1 EP 2010060603 W EP2010060603 W EP 2010060603W WO 2012010205 A1 WO2012010205 A1 WO 2012010205A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- instruction
- key
- encrypted
- value
- current
- Prior art date
Links
Classifications
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/52—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems during program execution, e.g. stack integrity ; Preventing unwanted data erasure; Buffer overflow
- G06F21/54—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems during program execution, e.g. stack integrity ; Preventing unwanted data erasure; Buffer overflow by adding security routines or objects to programs
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/70—Protecting specific internal or peripheral components, in which the protection of a component leads to protection of the entire computer
- G06F21/71—Protecting specific internal or peripheral components, in which the protection of a component leads to protection of the entire computer to assure secure computing or processing of information
- G06F21/72—Protecting specific internal or peripheral components, in which the protection of a component leads to protection of the entire computer to assure secure computing or processing of information in cryptographic circuits
-
- G—PHYSICS
- G06—COMPUTING; CALCULATING OR COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F9/00—Arrangements for program control, e.g. control units
- G06F9/06—Arrangements for program control, e.g. control units using stored programs, i.e. using an internal store of processing equipment to receive or retain programs
- G06F9/30—Arrangements for executing machine instructions, e.g. instruction decode
- G06F9/3017—Runtime instruction translation, e.g. macros
- G06F9/30178—Runtime instruction translation, e.g. macros of compressed or encrypted instructions
Definitions
- the present invention relates to the domain of software protection and more particularly to a device and a means for rendering software tamper-proof, thus ensuring the integrity of a piece of software.
- a typical system on which an application runs generally comprises a processing unit, a plurality of peripherals and memory.
- encryption schemes are used.
- information which is required to be kept secure, i.e. working data or executable code, is encrypted.
- Encryption is usually done within a security module, which forms part of the system.
- the security module can be implemented in a variety of manners such as on a microprocessor card, on a smartcard or any electronic module in the form of a badge or key.
- These modules are generally portable and detachable from the receiver and are designed to be tamper-proof.
- the most commonly used form has electrical contacts, but contactless versions of type ISO 14443 also exist.
- the security module exists where it is directly soldered inside the receiver, a variation of this being a circuit on a socket or connector such as a SIM module. Yet another implementation is to have the security module integrated on a chip which has another function e.g. on a de-scrambling module or on a microprocessor module of a decoder.
- the security module can also be implemented in software.
- Such analyses may lead to tampering whereby the software is modified by, for example, performing a branch-jamming attack wherein an unconditional jump is introduced in place of a conditional jump thus forcing a branch to execute when the current conditions do not prescribe such execution.
- a branch-jamming attack wherein an unconditional jump is introduced in place of a conditional jump thus forcing a branch to execute when the current conditions do not prescribe such execution.
- an attack would force a programme to bypass an authentication step like serial number or password checking for example.
- a code to call the decryption routine is placed inside each of the blocks and a programme controller to implement the dynamic integrity checking is added to the end of the programme. If an adversary tries to change a part of the programme, then the hash value for the block containing the changed part of the programme will be different and so the next block will not be properly decrypted and the programme crashes.
- the present invention allows for the executable code to exist in encrypted format, the encryption being done on an instruction by instruction basis and not requiring that the instructions be read twice.
- the scheme can be realised entirely in hardware with the inherent advantage that the encryption keys never appear anywhere where they might be vulnerable to being intercepted. There is no software overhead and therefore speed of execution is greatly increased.
- the encryption key for the next block depended only on the contents of a preceding block.
- the encryption key can depend on an accumulation of a number of preceding encryption key values. For example, the key to decrypt the next instruction could be based on the current instruction combined with an accumulation of the keys for the two previous instructions.
- the present invention aims to solve the problem of security caused through the analysis of software and the subsequent tampering of said software, while minimizing the overhead in order to achieve the solution and making it flexible and applicable to systems which use software of many different structure types.
- This is achieved using a processor-implemented method for ensuring the integrity of software in a programme memory, said software comprising a plurality of encrypted instructions, an instruction comprising at least an opcode, said method using an initialised instruction key and comprising the following steps:
- the invention can be applied to programmes whose structure is not necessarily tree-like in nature and may be realised in software or entirely in hardware thereby eliminating the possibility of a third party intercepting a decrypted instruction or a decryption key.
- FIG. 1 is a simplified block diagram of an embodiment of the present invention.
- - Fig. 2 shows a flow diagram of an embodiment of the present invention.
- - Fig. 3 is a simplified block diagram showing how software jumps or branches may be handled according to an embodiment of the present invention.
- the present invention aims to provide a means for running software in a secure manner whereby the software is stored in memory in encrypted form and decrypted and executed within a secure processor on an instruction by instruction basis, away from the possibility of being monitored.
- the key for the decryption of a current instruction depends on at least one previous instruction having been properly decoded, while the key for the decryption of a following instruction depends on the correct decryption of the current instruction. In this way, a self-checking means for guaranteeing the integrity of a piece of software is achieved.
- the mere successful execution of the software is a guarantee that neither the flow nor the content have been tampered with, since a modification made to one instruction would invalidate the ability to decrypt the following instruction, leading to premature termination of the programme or at least in a corruption of the programme execution trace.
- the scheme used in the present invention can be realised in software, but it is to be noted that it can be realised entirely in hardware, thereby removing the possibility of a third party intercepting instructions in clear or intercepting any of the decryption keys involved.
- the invention results in almost no overhead compared to solutions in the state of the art.
- the scheme can be applied to software of various different architectures or structures including those with jumps and breaks and is not limited to structures known as tree structures.
- the present invention therefore provides a method for ensuring tamper-proof software execution in a system comprising at least a programme memory (PMEM) to hold encrypted programme instructions (INSTP', INSTC, INSTF'), a decryption module (DECR) to decrypt said programme instructions, a data processing unit (SCPU) to execute the decrypted programme instructions (INSTP, I NSTC, I NSTF) and a means to build decryption keys, known as instruction keys (KP, KC, KF), to decrypt the encrypted programme instructions.
- the means for building the instruction keys could of course reside within the data processing unit.
- the decryption module and the data processing unit are to reside preferably within a security module of any of the types which are well- known in the state of the art.
- the current encrypted instruction is read from the programme memory (PMEM) and is decrypted (DECR) to give a current instruction (INSTC) using a current decryption key (KC) which is built from a combination (Fn) of on one hand a digest of the previous decryption key (KP) and on the other hand a digest of the previously executed instruction (DIG(INSTRP)), as shown in Fig. 1 .
- digest it is meant any operation applied to all or part of an operand and yielding an output. It is worth noting that the digest, when performed on an operand, may yield an output which is equal to the operand itself.
- the digest includes a one-way function on the operand. This allows for further hampering any attempt by a third party to work back and deduce previous keys or previous instructions.
- a hash function is an example of such a one-way function (SHA2, MD5 for example).
- SHA2, MD5 for example
- “combination” it is meant any form of combination of the mentioned operands whether it be logical or arithmetical or cryptographic.
- KC current decryption key
- Fig. 2 shows a flow diagram representing the above embodiment of the present invention.
- This representation describes the invention from the point of view of a snapshot in time, rather than speaking of a current instruction with its current decryption key and a previous instruction with its previous key etc, it refers only to an instruction key (Kl) which is updated as each instruction is executed.
- a programme counter (PC) is used to indicate the location of the next instruction to be executed.
- the programme counter is incremented following the execution of an instruction or otherwise updated if said instruction dictates a different form of update other than a simple increment. For example, if an instruction involves a command to load a value from a register, then the programme counter will usually simply be incremented to indicate the following location. However, if the instruction involves a jump to a certain location, then the program counter will be updated with the value of the location indicated by the jump.
- the programme counter (PC) and the instruction key (Kl) are first initialised (INI PC, INI Kl).
- An encrypted instruction is read from the programme memory at a location indicated by the programme counter (RD INST' c.f. PC) and decrypted using the instruction key (DCPT INST, Kl).
- the instruction is executed (EX INST) and the programme counter is updated (UPD PC) either by a simple increment or by substituting a new value as dictated by the instruction.
- the instruction key is updated (UPD Kl, INST) using a digest of the executed instruction. The updating of the instruction key therefore takes into account not only the instruction which has just been executed but also the value of the key which was used to decrypt the instruction.
- the instruction key which was previously used to decrypt the previous instruction was built from the previous instruction and the instruction key which was used to decrypt the instruction before that.
- the value of the instruction key not only depends on the last executed instruction but on all previously executed instructions combined.
- the updating of the instruction key takes into account the value of the last executed instruction and the values of at least the two preceding executed instructions.
- the key for decrypting instruction 4 could be a combination of a digest of instruction 3, a digest of instruction 2 and a digest of instruction 1.
- the method of the present invention involves a loop wherein the instruction key is updated using the previously executed instruction. This leads to the question as to how to decrypt the first instruction in a programme.
- the first instruction in a programme is left in clear while all other instructions are encrypted.
- the first instruction is therefore executed directly, thereby beginning the loop, and the second instruction is decrypted using an instruction key based on the first instruction and so on.
- the entire programme is encrypted, including the first instruction, and the instruction key is initialised using a value which will decrypt the first instruction. This value could be a master key which is built into the security module or otherwise communicated to the security module from outside.
- a current instruction residing at a current memory location (C) may be referenced by more than one previous instructions (INSTP1 , INSTP2).
- INSTP1 , INSTP2 a current instruction, or callee
- INSTC current instruction
- INSTP1 , INSTP2 a current instruction, or callee
- INSTC current instruction
- INSTP2 branch-type instruction
- INSTC callee
- CORR1 CORR2
- CORR2 CORR2
- the instruction key required to properly decrypt the encrypted instruction at location C is KCIN-
- the value of the instruction key following the execution of the instruction resident at P1 is ⁇ ⁇
- the value of the instruction key following the execution of the instruction resident at P2 is ⁇ 2 0 ⁇ -
- ⁇ ⁇ is not equal to ⁇ 2 ⁇
- neither KPI ouT nor KP2OUT are equal to KCIN-
- the method therefore requires that a modification (CORR1 , CORR2) be made thus allowing the instruction key value to be brought to the necessary value whenever a branch-type of instruction is executed. Since the value of the key required to decrypt the callee is known (i.e.
- the modification value is introduced as a further operand in the combination of the previous decryption key and the digest of the previous instruction as described above.
- a jump instruction comprises a destination parameter, as is usually the case for a jump instruction, and further comprises a modification parameter, e.g. JMP C, #CORR1.
- the modification value (#CORR1 ) is then used as an additional parameter in the combination of the previous instruction key and all or part of the previous instruction. It is useful to note that rather than extracting the modification value from the instruction and using it as an extra parameter in the combination step, the digest of the jump instruction could already take the modification value into account.
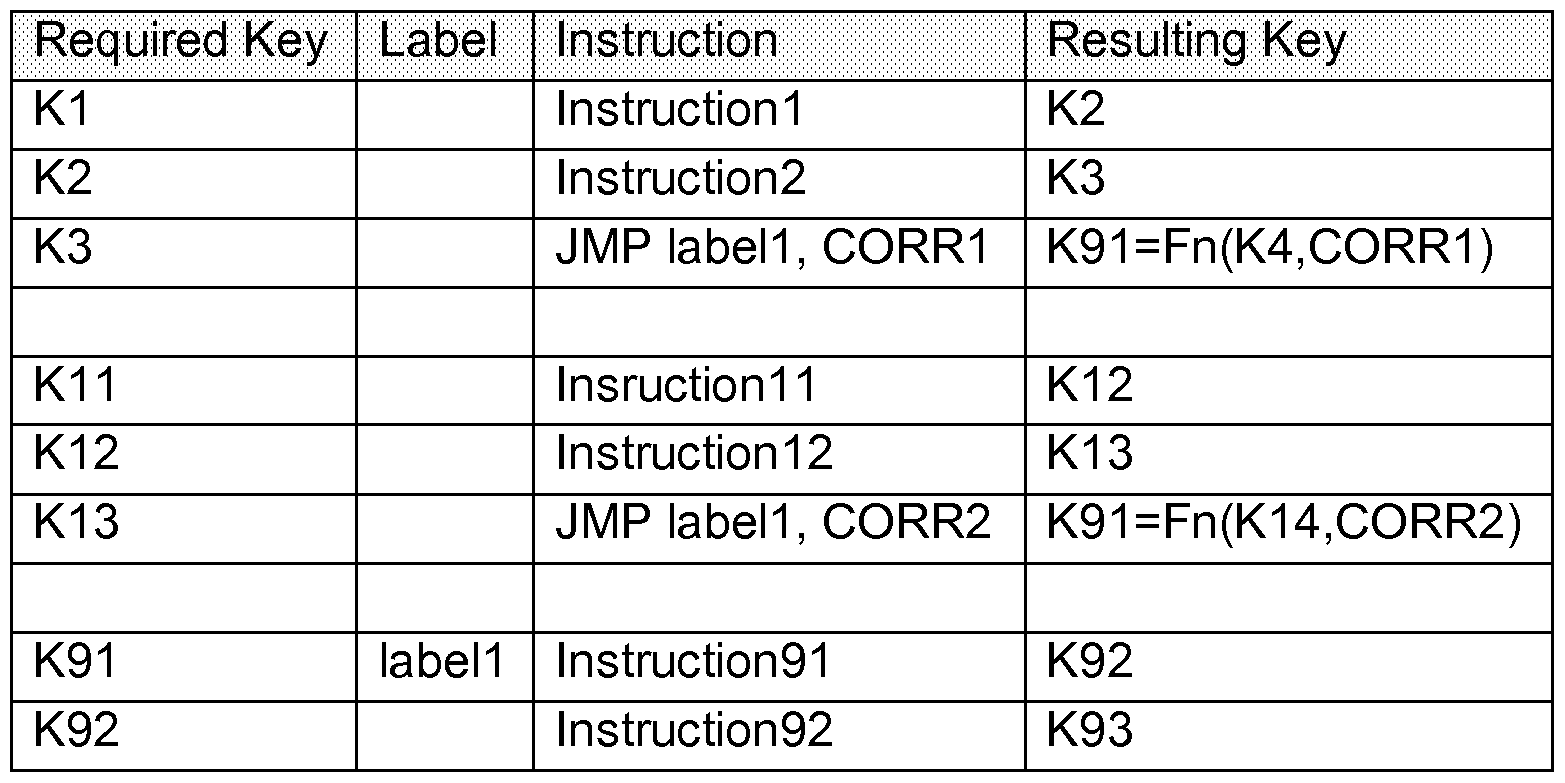
- the following table T1 illustrates the state of the instruction keys as the execution of a programme evolves through a modified jump instruction of the type described above.
- the table includes the value of the key required to decrypt an instruction and the value of the key following the execution of the instruction and the calculation of a new key. Since the value of the key required to decrypt the instruction at labeH is known, it follows that the appropriate correction values, CORR1 or CORR2, can be calculated in order to bring the unmodified values, K4 or K14, to the required value K91 .
- a standard jump instruction is used and the modification to the instruction key described above is done by a dedicated "modifying" instruction with a modification value as a parameter.
- the function of such a modification instruction is to act directly upon the instruction key based on the modification value.
- the modifying instruction is placed just before the branch or jump type instruction, thus allowing for the instruction key to be appropriately updated in order to properly decrypt the callee.
- the "modification" function as described above may in actual fact be a plurality of instructions which are designed to perform the desired modifying operation on the value of the instruction key.
- the instruction key at the callee "labeH " has the value K91 . Due to the fact that the program flow can arrive from different paths, a correction instruction lnst_CORR is added just before the jump so that the instruction key is updated to a predetermined value K90.
- the execution of the branch-type instruction which in this case is a jump, will modify the instruction key from K90 to K91.
- the correction value (C1 , C2) associated with the correction instruction (lnst_CORR) aims to modify the current i nstruction key (K3, K1 3) to the predefined value K90.
- the execution of the jump will update the instruction key from K90 to K91 , the value used to decrypt the instruction at the callee (labeH ).
- the correction value C3 attached to the correction instruction lnst_CORR should take into account the difference and the instruction key while executing the branch instruction will not be the same as for the jump instruction. However, due to the correction value C3, the final value after the execution of the short branch instruction will still be K91.
- the following table T3 illustrates the state of the instruction keys as the execution of a programme evolves through a conditional jump instruction, where two different destinations, labeM and Iabel2, are possible following the execution of the conditional jump.
- the key required to decrypt the instructions at both destinations should be the same.
- the table includes the value of the key required to decrypt an instruction and the value of the key following the execution of the instruction and the calculation of a new key.
- parameters can be passed during the call thereby increasing the number of possible different flows within the function or subroutine and consequently the number of possible outcomes following the execution of the function or subroutine.
- a modification is made to the instruction key so that its state may be known at the beginning of the function or subroutine and a further modification is made upon returning from the call i.e. just before coming out of the function or subroutine.
- the modification as described above could also simply entail a substitution of one key by another key.
- an instruction comprises at least an opcode, defining an operation to be performed.
- the instruction may comprise no more than this or it may further comprise one or a plurality of operands on which the operation is to be performed.
- an instruction may comprise an authentication tag, otherwise known as an integrity figure, which is used as a way of checking the validity of the i nstruction. Consequently, in another embodiment of the present invention, before the execution of an instruction, the instruction may first be verified using an authentication tag as described above.
- the authentication tag may take the form of a checksum or a hash value of all or part of the opcode and operand(s).
- the authentication tag may be regarded as a signature of the opcode.
- the method used in this embodiment of the present invention therefore comprises reading a current encrypted instruction; using the instruction key to decrypt the current encrypted instruction and the authentication tag; verifying the thus extracted authentication tag; updating the instruction key using a calculation based on the current value of the instruction key (or a digest thereof) and a digest of the current instruction, so that the next encrypted instruction to be read may be decrypted with the updated instruction key; executing the current instruction on condition that the authentication tag was found to be valid. If the authentication tag is not found to be valid, then the programme may be made to terminate gracefully i.e. while generating an appropriate alarm.
- an objective may not necessarily be to prevent a third party from being able to copy a piece of software but merely to prevent that third party from altering the software without such alteration being detected
- one embodiment of the invention exists wherein the opcodes of the instructions are left in clear and only the authentication tags are encrypted. This is sufficient to achieve the goal of guaranteeing software integrity afforded by the invention. Similarly it is possible in another embodiment to encrypt only the operands should they exist. Likewise, encryption of any of opcode, operands or authentication tags or any other combination thereof is possible.
- the present invention therefore provides a sol uti on to the problem of guaranteeing the integrity of software programmes by encrypting all or part of each instruction of a programme using a key based on all or part of one or a plurality of previous instructions, thus resulting in a different encryption key per instruction.
- the invention is applicable to software programmes whose structures are not necessarily tree-like in nature and is also applicable when the programme includes loops, jumps, calls or breaks etc.
- the invention allows for an exception to be flagged when an encrypted instruction is wrongly decrypted.
- the first instruction does not necessarily have to be in clear since the instruction key may be appropriately initialised as required.
- the invention can be realised in software or entirely in hardware thereby eliminating the possibility of a third party intercepting a decrypted instruction or a decryption key.
- the encryption of the instruction can use one of a large range of encryption algorithms such as a stream cipher, a block cipher, a one-time pad, a scrambler such as bit inversion, bit shifting, bit swapping, parity algorithm or cyclic redundancy code for example.
Abstract
Description
Claims
Priority Applications (6)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2013519968A JP5616528B2 (en) | 2010-07-22 | 2010-07-22 | A method implemented by a processor for ensuring the integrity of software |
| PCT/EP2010/060603 WO2012010205A1 (en) | 2010-07-22 | 2010-07-22 | A processor-implemented method for ensuring software integrity |
| CN201080067681.3A CN102959556B (en) | 2010-07-22 | 2010-07-22 | For guaranteeing the method that the processor of software integrity realizes |
| KR1020127031855A KR101687439B1 (en) | 2010-07-22 | 2010-07-22 | A processor-implemented method for ensuring software integrity |
| RU2013104050/08A RU2541196C2 (en) | 2010-07-22 | 2010-07-22 | Method of providing software integrity |
| BR112012031052-6A BR112012031052B1 (en) | 2010-07-22 | 2010-07-22 | method implemented by a processor aimed at ensuring the integrity of the software |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| PCT/EP2010/060603 WO2012010205A1 (en) | 2010-07-22 | 2010-07-22 | A processor-implemented method for ensuring software integrity |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2012010205A1 true WO2012010205A1 (en) | 2012-01-26 |
Family
ID=43297003
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/EP2010/060603 WO2012010205A1 (en) | 2010-07-22 | 2010-07-22 | A processor-implemented method for ensuring software integrity |
Country Status (6)
| Country | Link |
|---|---|
| JP (1) | JP5616528B2 (en) |
| KR (1) | KR101687439B1 (en) |
| CN (1) | CN102959556B (en) |
| BR (1) | BR112012031052B1 (en) |
| RU (1) | RU2541196C2 (en) |
| WO (1) | WO2012010205A1 (en) |
Cited By (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2017014890A1 (en) * | 2015-07-20 | 2017-01-26 | Intel Corporation | Technologies for integrity, anti-replay, and authenticity assurance for i/o data |
| US20170024569A1 (en) * | 2015-07-20 | 2017-01-26 | Intel Corporation | Technologies for secure trusted i/o access control |
| FR3071121A1 (en) * | 2017-09-14 | 2019-03-15 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | METHOD FOR EXECUTING A BINARY CODE OF A FUNCTION SECURE BY A MICROPROCESSOR |
| EP3712794A1 (en) | 2019-03-21 | 2020-09-23 | Commissariat à l'énergie atomique et aux énergies alternatives | Method for executing a binary code of a function secured by a microprocessor |
| US10942868B2 (en) | 2017-09-14 | 2021-03-09 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | Execution process of binary code of function secured by microprocessor |
| EP4002165A1 (en) * | 2020-11-18 | 2022-05-25 | Thales DIS France SA | Code flow protection with error propagation |
Families Citing this family (8)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103902858A (en) * | 2013-12-25 | 2014-07-02 | 武汉安天信息技术有限责任公司 | APK application reinforcing method and system |
| JP6478724B2 (en) * | 2015-03-09 | 2019-03-06 | Kddi株式会社 | Information processing apparatus, information processing method, and computer program |
| CN106789006A (en) * | 2016-11-28 | 2017-05-31 | 范睿心 | A kind of decryption method and system |
| KR101953444B1 (en) * | 2016-12-26 | 2019-05-17 | 포항공과대학교 산학협력단 | Software security method based on virtualization technologies to ensure the security level equivalent to hardware and system using the same |
| RU179302U1 (en) * | 2017-11-21 | 2018-05-07 | Александра Владимировна Харжевская | DEVICE OF DYNAMIC CONTROL OF PERFORMANCE OF SPECIAL COMPUTATIONS |
| CN110515652B (en) * | 2019-08-30 | 2021-10-15 | 腾讯科技(深圳)有限公司 | Code abstract generation method and device and storage medium |
| CN111565002A (en) * | 2020-05-22 | 2020-08-21 | 北京合康新能变频技术有限公司 | Control system of frequency converter |
| CN111881467B (en) * | 2020-06-12 | 2022-10-28 | 海光信息技术股份有限公司 | Method and device for protecting file by using security processor, CPU and computer equipment |
Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5675645A (en) * | 1995-04-18 | 1997-10-07 | Ricoh Company, Ltd. | Method and apparatus for securing executable programs against copying |
| EP0908810A2 (en) * | 1997-10-10 | 1999-04-14 | General Instrument Corporation | Secure processor with external memory using block chaining and block re-ordering |
| WO2004072891A2 (en) * | 2003-02-11 | 2004-08-26 | Vi Laboratories, Llc | System and method for regulating execution of computer software |
Family Cites Families (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP2002353960A (en) * | 2001-05-30 | 2002-12-06 | Fujitsu Ltd | Code performing device and code distributing method |
| US6715085B2 (en) * | 2002-04-18 | 2004-03-30 | International Business Machines Corporation | Initializing, maintaining, updating and recovering secure operation within an integrated system employing a data access control function |
| US6948067B2 (en) * | 2002-07-24 | 2005-09-20 | Qualcomm, Inc. | Efficient encryption and authentication for data processing systems |
| US7103779B2 (en) * | 2003-09-18 | 2006-09-05 | Apple Computer, Inc. | Method and apparatus for incremental code signing |
| EP1855476A3 (en) * | 2006-05-11 | 2010-10-27 | Broadcom Corporation | System and method for trusted data processing |
| KR100922862B1 (en) * | 2007-11-14 | 2009-10-20 | 성균관대학교산학협력단 | Security method of system by? encoding instructions |
| CN101452514B (en) * | 2007-12-06 | 2011-06-29 | 中国长城计算机深圳股份有限公司 | User data protection method for safety computer |
| JP2009211292A (en) * | 2008-03-03 | 2009-09-17 | Oki Electric Ind Co Ltd | Encryption method, decryption method, encryption device, and decryption device |
| EP2196937A1 (en) * | 2008-12-15 | 2010-06-16 | Thomson Licensing | Methods and devices for instruction level software encryption |
-
2010
- 2010-07-22 KR KR1020127031855A patent/KR101687439B1/en active IP Right Grant
- 2010-07-22 CN CN201080067681.3A patent/CN102959556B/en active Active
- 2010-07-22 WO PCT/EP2010/060603 patent/WO2012010205A1/en active Application Filing
- 2010-07-22 RU RU2013104050/08A patent/RU2541196C2/en not_active IP Right Cessation
- 2010-07-22 BR BR112012031052-6A patent/BR112012031052B1/en active IP Right Grant
- 2010-07-22 JP JP2013519968A patent/JP5616528B2/en active Active
Patent Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5675645A (en) * | 1995-04-18 | 1997-10-07 | Ricoh Company, Ltd. | Method and apparatus for securing executable programs against copying |
| EP0908810A2 (en) * | 1997-10-10 | 1999-04-14 | General Instrument Corporation | Secure processor with external memory using block chaining and block re-ordering |
| WO2004072891A2 (en) * | 2003-02-11 | 2004-08-26 | Vi Laboratories, Llc | System and method for regulating execution of computer software |
Cited By (13)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US10552619B2 (en) * | 2015-07-20 | 2020-02-04 | Intel Corporation | Technologies for secure trusted I/O access control |
| US20170024569A1 (en) * | 2015-07-20 | 2017-01-26 | Intel Corporation | Technologies for secure trusted i/o access control |
| US10073977B2 (en) | 2015-07-20 | 2018-09-11 | Intel Corporation | Technologies for integrity, anti-replay, and authenticity assurance for I/O data |
| WO2017014890A1 (en) * | 2015-07-20 | 2017-01-26 | Intel Corporation | Technologies for integrity, anti-replay, and authenticity assurance for i/o data |
| US10650151B2 (en) | 2017-09-14 | 2020-05-12 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | Method of execution of a binary code of a secure function by a microprocessor |
| EP3457620A1 (en) * | 2017-09-14 | 2019-03-20 | Commissariat à l'Énergie Atomique et aux Énergies Alternatives | Method for executing a binary code of a secure function by a microprocessor |
| FR3071121A1 (en) * | 2017-09-14 | 2019-03-15 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | METHOD FOR EXECUTING A BINARY CODE OF A FUNCTION SECURE BY A MICROPROCESSOR |
| US10942868B2 (en) | 2017-09-14 | 2021-03-09 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | Execution process of binary code of function secured by microprocessor |
| EP3712794A1 (en) | 2019-03-21 | 2020-09-23 | Commissariat à l'énergie atomique et aux énergies alternatives | Method for executing a binary code of a function secured by a microprocessor |
| FR3094107A1 (en) | 2019-03-21 | 2020-09-25 | Commissariat à l'Energie Atomique et aux Energies Alternatives | PROCESS FOR EXECUTING A BINARY CODE OF A SECURE FUNCTION BY A MICROPROCESSOR |
| US11461476B2 (en) | 2019-03-21 | 2022-10-04 | Commissariat A L'energie Atomique Et Aux Energies Alternatives | Method for executing a binary code of a function secured by a microprocessor |
| EP4002165A1 (en) * | 2020-11-18 | 2022-05-25 | Thales DIS France SA | Code flow protection with error propagation |
| WO2022106229A1 (en) * | 2020-11-18 | 2022-05-27 | Thales Dis France Sas | Code flow protection with error propagation |
Also Published As
| Publication number | Publication date |
|---|---|
| KR20130120985A (en) | 2013-11-05 |
| RU2541196C2 (en) | 2015-02-10 |
| CN102959556B (en) | 2015-12-16 |
| BR112012031052A2 (en) | 2016-10-25 |
| JP2013535725A (en) | 2013-09-12 |
| KR101687439B1 (en) | 2016-12-16 |
| BR112012031052B1 (en) | 2020-12-01 |
| CN102959556A (en) | 2013-03-06 |
| JP5616528B2 (en) | 2014-10-29 |
| RU2013104050A (en) | 2014-08-27 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US8683224B2 (en) | Processor-implemented method for ensuring software integrity | |
| WO2012010205A1 (en) | A processor-implemented method for ensuring software integrity | |
| CN111052115B (en) | Data processing apparatus and method of authentication depending on call path | |
| Lee et al. | Architecture for protecting critical secrets in microprocessors | |
| US8949586B2 (en) | System and method for authenticating computer system boot instructions during booting by using a public key associated with a processor and a monitoring device | |
| US10223117B2 (en) | Execution flow protection in microcontrollers | |
| CN109409086B (en) | Device for detecting falsified return address in stack based on newly added instruction | |
| US20170046280A1 (en) | Data processing device and method for protecting a data processing device against attacks | |
| KR100922862B1 (en) | Security method of system by? encoding instructions | |
| EP0962850A2 (en) | A method for protecting embedded system software and embedded system | |
| US20230017231A1 (en) | Securely executing software based on cryptographically verified instructions | |
| CN109409083B (en) | Device for detecting return address tampering in stack | |
| CA2958986C (en) | System and method for protecting a device against attacks on processing flow using a code pointer complement | |
| KR100978605B1 (en) | Attack detecting method and attack detect0r for system security | |
| CN114816549B (en) | Method and system for protecting bootloader and environment variable thereof | |
| US8555387B2 (en) | Apparatus and method for protecting asset in computer system | |
| CN117786699A (en) | Chip initialization method, device, module, electronic equipment and storage medium | |
| CN117378170A (en) | Enhanced cryptography system and method | |
| EP2975549A1 (en) | Method and device to protect software code against fault attack | |
| JP2004280678A (en) | Data processor and data processing method | |
| Patel et al. | CUFFS: An instruction count based architectural framework for security of MPSoCs |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| WWE | Wipo information: entry into national phase |
Ref document number: 201080067681.3 Country of ref document: CN |
|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 10737543 Country of ref document: EP Kind code of ref document: A1 |
|
| ENP | Entry into the national phase |
Ref document number: 20127031855 Country of ref document: KR Kind code of ref document: A |
|
| ENP | Entry into the national phase |
Ref document number: 2013519968 Country of ref document: JP Kind code of ref document: A |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| ENP | Entry into the national phase |
Ref document number: 2013104050 Country of ref document: RU Kind code of ref document: A |
|
| 122 | Ep: pct application non-entry in european phase |
Ref document number: 10737543 Country of ref document: EP Kind code of ref document: A1 |
|
| REG | Reference to national code |
Ref country code: BR Ref legal event code: B01A Ref document number: 112012031052 Country of ref document: BR |
|
| ENP | Entry into the national phase |
Ref document number: 112012031052 Country of ref document: BR Kind code of ref document: A2 Effective date: 20121205 |